- From journalists and civil society organizations to regular individuals with online privacy concerns, Tor Browser users are a diverse group.
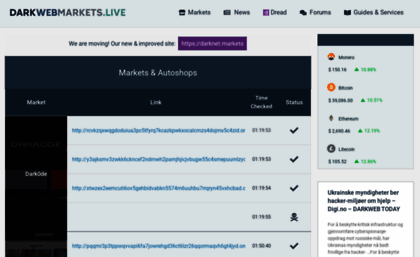
- It's divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media).
- Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy.
- Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
- The inconvenience of the darknet infrastructure is outweighed by the security it provides.
- If it came out early enough, it might have even slowed down the greed of ad-revenue-based sites from practically ruining the net like a plague of locusts.
The .onion dark web is a hidden part of the internet that is often misunderstood. While it has gained notoriety for illegal activities, it also serves crucial purposes for privacy and freedom of expression. Understanding this obscure online space is vital for anyone seeking to navigate the digital landscape safely and responsibly. This article will explore what the .onion dark web is, how it functions, its uses, and the necessary precautions to take if one chooses to explore it.
Examples of the deep web include any websites that are behind a paywall or require login credentials. The deep web refers to any web content that is not indexed or pages that can’t be found with a search engine. Webpages on the open web will show up in search results on sites like Google and Bing. The sharing of illegal pornography and discussion of illegal sex acts account for a significant portion of dark web traffic. In March 2012 Russian hacker Yevgeniy Nikulin and three accomplices stole passwords for 117 million e-mail addresses from the social media company LinkedIn and then offered the data for sale on the dark web. As hoped, the Tor anonymous network grew in popularity among computer enthusiasts, privacy advocates, journalists, dissidents under repressive governments, and others desirous of strict secrecy.
This process is ineffective on the dark and deep web, where most sites are not interlinked. For businesses and cybersecurity professionals, however, they are a critical instrument. Yet some of today’s biggest risks—such as data breaches, identity theft, and corporate espionage—often originate on the dark web. Traditional security tools are designed to stop known threats.
.onion Dark Web
The .onion domain is part of a larger network known as Tor (The Onion Router). This network employs multiple layers of encryption, ensuring that users' identities and locations remain concealed. By routing internet traffic through a series of volunteer-operated servers (or nodes), Tor makes it challenging to trace activities back to individuals. This characteristic of anonymity is what makes the .onion dark web attractive to those seeking privacy.
How Does it Work?
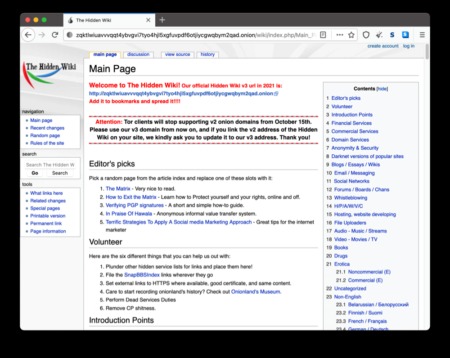
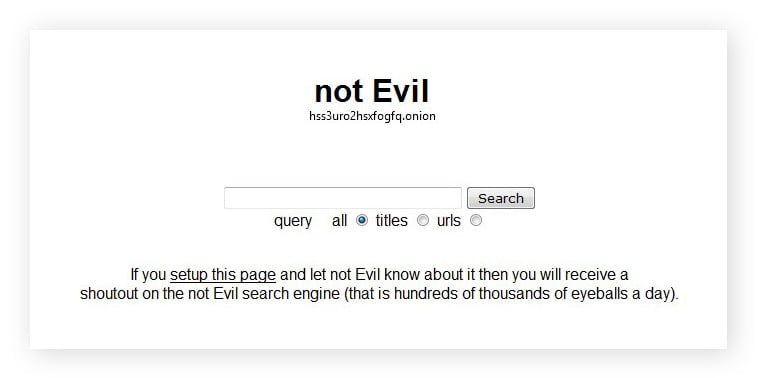
To access the .onion sites, users must download the Tor browser, which is designed to connect to the Tor network. Once installed, users can access websites with the .onion domain that are not indexed by traditional search engines. These sites can range from forums and blogs to marketplaces and information resources. It’s important to note that while some content found on the .onion dark web can be illegal, there are also legitimate sites that provide valuable information and support to users in oppressive regimes.

Legitimate Uses of the .onion Dark Web
While the .onion dark web is often associated with illicit activities, it has several legitimate uses. Here are a few:
- Privacy Protection: Journalists and activists use the dark web to communicate securely and protect their identities, especially in countries with heavy censorship.
- Whistleblower Platforms: Sites like SecureDrop allow whistleblowers to share information confidentially with media organizations.
- Support Communities: Numerous forums cater to marginalized groups, providing a safe space for discussions on sensitive topics without fear of retribution.
Risks and Precautions
Despite its positive aspects, navigating the .onion dark web comes with significant risks. Here are some precautions to consider:
- Stay Informed: Familiarize yourself with the potential dangers associated with the dark web, including scams and malicious software.
- Use VPN Services: Complement your Tor browser usage with a Virtual Private Network (VPN) for added security.
- Avoid Sharing Personal Information: Always protect your identity by refraining from sharing personal data, even on legitimate sites.
Conclusion
The .onion dark web is a complex realm that offers both opportunities and dangers. By understanding how it works and the diverse uses it serves, individuals can better navigate this hidden space. Whether for legitimate purposes or academic inquiry, knowledge about the .onion dark web is essential in today’s digital age. Always prioritize safety and remain vigilant while exploring its depths.