The dark web is often shrouded in mystery, sparking both intrigue and concern in equal measure. This hidden part of the internet offers a wealth of information, but its reputation for illegal activities can create a misleading perception. Understanding access to the dark web is crucial for those who wish to navigate it safely and responsibly. This article aims to enlighten readers about what the dark web is, how to access it, and the potential dangers that lurk within its depths.
It’s critical to use a Dark Web monitoring solution that can keep a continuous eye on your adversaries and engage with threat actors. Monitor exclusive dark web forums and the private channels of threat actors. Go behind enemy lines to identify threat actors and their intentions at the earliest stages so you can properly prepare your defenses. This is particularly true for enterprise organizations working with sensitive data in key sectors like healthcare, energy, and finance. Threat intelligence gathered from the Deep and Dark Web is likely to help future threat hunting teams when analyzing telemetry from beyond their own networks, such as the Deep and Dark Web. Therefore, it’s likely that not all deep- and dark-web file repositories represent good intentions.
Many transactions on the dark web use cryptocurrencies like Bitcoin for anonymity. You can also use a password manager to generate and store complex passwords with ease. Avoid using the same password across multiple sites since it increases your vulnerability if one account is compromised. Maintain a high level of anonymity by using pseudonyms and encrypted communication whenever possible.
What is the Dark Web?
The dark web is a subset of the deep web, which encompasses parts of the internet not indexed by traditional search engines. While the deep web includes benign topics such as academic databases and subscription services, the dark web is often associated with anonymity and illicit activities. It is accessed through special software, ensuring user privacy and security.
Understanding the Surface, Deep, and Dark Web
To comprehend access to the dark web, it's essential to differentiate between the surface web, deep web, and dark web:
- Surface Web: This includes all web pages indexed by search engines, constituting only a small fraction of the total internet.
- Deep Web: Comprises vast amounts of data not indexed, such as private databases, academic resources, and medical records.
- Dark Web: Represents a portion of the deep web that is intentionally hidden, requiring specific tools to access.
How to Access the Dark Web
Gaining access to the dark web requires a few key steps, which should be approached with caution. Here’s how you can start:
- Download Tor Browser: The most common way to access the dark web is through the Tor browser, which anonymizes your internet connection.
- Utilize a VPN: While Tor provides anonymity, pairing it with a Virtual Private Network (VPN) adds an extra layer of security, protecting your location and identity.
- Secure Your Device: Ensure your device has updated antivirus software and a reliable firewall to guard against potential threats.
- Access via Specific URLs: Dark web sites often have .onion addresses. Use trusted sources for links, as many sites can be harmful.
Potential Risks of the Dark Web

While exploring access to the dark web can be intriguing, it comes with significant risks that users must be aware of:
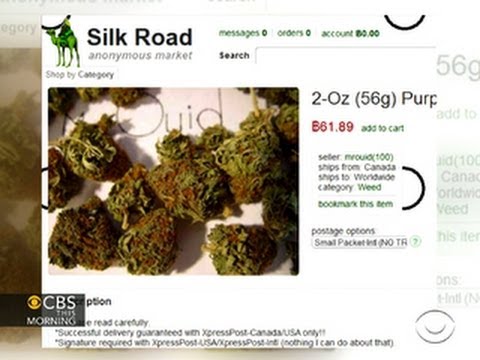
- Legal Consequences: Some content and activities on the dark web are illegal, and users may inadvertently find themselves violating laws.
- Scams and Fraud: Many dark web sites operate scams, and users risk losing sensitive information or funds.
- Cybersecurity Threats: The dark web can harbor malware and hackers looking to exploit vulnerabilities in users’ systems.
Staying Safe on the Dark Web
For those who choose to navigate the dark web, safety precautions are paramount. Here are some tips to stay secure:
- It grew from a research program into the most widely trusted tool for anonymous browsing.
- A VPN is helpful when you want to hide the fact that you’re connecting to Tor from your internet provider.
- Torch is one of the more established dark web search engines, designed to help users navigate the Tor network and discover onion sites.
- Even if Google tried, site operators could block standard crawlers.
- Limit Personal Information: Avoid sharing any personal data. Anonymity is key to protecting your identity.
- Be Skeptical: Verify the credibility of sites and offers before engaging. Trust your instincts; if something feels wrong, it probably is.
- Stay Informed: Keep abreast of dark web trends and known threats to help mitigate risks.
Conclusion
The allure of the dark web is often accompanied by a range of risks and misconceptions. By understanding access to the dark web, individuals can make informed choices about whether to explore this hidden facet of the internet. Knowledge is a powerful tool in remaining safe and secure online, enabling users to navigate the digital world responsibly.