In an increasingly digital world, understanding the various layers of the internet is essential for users of all backgrounds. While most individuals use the internet for everyday activities, there is a more concealed part known as the darknet. This article will explore how to access darknet on iPhone, providing essential information for those looking to navigate this less conventional space safely and responsibly.
As a small part of the deep web, operators of the dark web keep it hidden on purpose. However, staying safe on the dark web depends on you – use the right tools, stay alert, and always put security first. While the dark web can be a risky place, it remains an essential part of the internet for those seeking true digital privacy. The demand for privacy-focused online experiences has contributed to the continued growth and relevance of the dark web.
It's still possible to track someone's traffic pinging through the Tor nodes, though it is difficult. With any security and privacy issue, it's about your threat model, which is simply what attacks or invasions you're actually worried about. "Contrary to what most people think, these modes do not actually protect your privacy," she says. Once you've downloaded and installed the Tor browser, you can browse just as you would your usual browser, but Muffett offers a caveat to avoid unencrypted sites — those with only "http" in the URL rather than "HTTPS". Slide up to the "safest" level, and as well as those settings, JavaScript is disabled on all sites. In "safer" mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won't run automatically, you'll have to click to play.
Understanding the Darknet
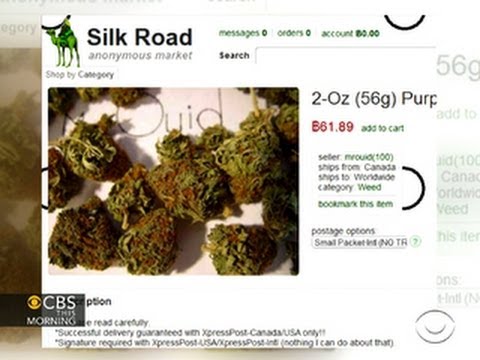
The darknet is a part of the internet that is not indexed by traditional search engines. It is often associated with anonymity and privacy, attracting users who seek to escape censorship, engage in private communications, or access materials that may not be available on the surface web. However, navigating this segment requires caution and the right tools.
Why Access Darknet on iPhone?
Using an iPhone to access the darknet may appeal to users seeking mobility and convenience. The stability, security features, and privacy controls of iOS devices make them attractive for cautious browsing. It is important to note that while there are valid reasons for accessing the darknet, users should always prioritize safety and ethical considerations.

Necessary Tools and Preparations

To access darknet on iPhone, specific tools are required. The most common method involves using the TOR network, which allows users to browse anonymously. Here’s how to get started:
Step 1: Install the TOR Browser
Although an official TOR browser application is not available for iOS, users can utilize the Onion Browser, a reputable option. Download it from the App Store and familiarize yourself with the settings. The Onion Browser routes your internet traffic through the TOR network, providing anonymity during your browsing session.
Step 2: Configure Security Settings
Before accessing the darknet, it is crucial to adjust your privacy settings. Within the Onion Browser, make sure that the security level is set to the highest option. This protects you from potential threats and ensures you have a safer browsing experience.
Step 3: Use a VPN
For added security, consider using a Virtual Private Network (VPN). A VPN encrypts your internet connection and masks your IP address, further enhancing your anonymity. Choose a reputable VPN provider, and connect it before launching the Onion Browser.
Navigating the Darknet Safely
Once you’re set up, it’s time to explore. Keep in mind that the darknet is a mixed bag; while you can find valuable information, there are also risks involved, such as malicious sites or illegal content. Here are some safety tips:
- Although the surface web only comprises about 4-5% of the entire internet, scope is important to keep in mind because this is still impressively expansive.
- If one is careful, most of the legitimate onion services present very little risk.
- There are both free and paid VPN services, but if you’re planning on accessing the dark web, you’re going to want to opt for a high-quality paid VPN that offers you plenty of protection.
- Of course, always follow the usual recommendations for safer online behavior, like never downloading files or clicking on links from untrusted sources.
- So if we see just 10% of what’s actually on the internet, where is the rest of it?
- The Tor Browser automatically starts Tor background processes and routes traffic through the Tor network.
- Stay informed: Understand the resources or websites you are engaging with.
- Avoid sharing personal information: Remain vigilant about your identity and digital footprint.
- Engage ethically: Use your access responsibly and be aware of the consequences of your actions.
Conclusion
- With any security and privacy issue, it's about your threat model, which is simply what attacks or invasions you're actually worried about.
- Attackers used this vulnerability to extract users' MAC and IP addresses and Windows computer names.
- Concerns raised included the role of an academic institution in policing, sensitive research involving non-consenting users, the non-targeted nature of the attack, and the lack of disclosure about the incident.
- Indeed, cyber breaches have shown us that any backdoor or weakness can be found and exploited by hackers in order to steel people’s information, pictures and data.
- This info will help you prevent repeat performances and may be needed for legal or regulatory disclosures.
Accessing the darknet on an iPhone can provide users with unique opportunities and resources. However, it is vital to approach this hidden part of the internet with caution, ensuring you remain informed and secure. By utilizing tools like the Onion Browser and VPNs, you can navigate the darknet with a greater sense of privacy and safety. Always remember to act responsibly and ethically in your browsing habits, recognizing the implications of your actions in this complex digital landscape.